HashiCorp Terraform Unveils New Cost Analytics and Enhanced Governance Controls
Introduction
In recent months, the HashiCorp Terraform engineering team has delivered a series of feature updates aimed at eliminating infrastructure blind spots and strengthening governance and security across the entire infrastructure lifecycle. The latest improvements for HCP Terraform and Terraform Enterprise include general availability of billable resource analytics, project-level remote state sharing, module testing for dynamic credentials, project-level notifications, and a beta for registry tagging. These capabilities give platform teams better visibility, control, and cost management.
Billable Resource Analytics Now Generally Available
Addressing the Visibility Gap
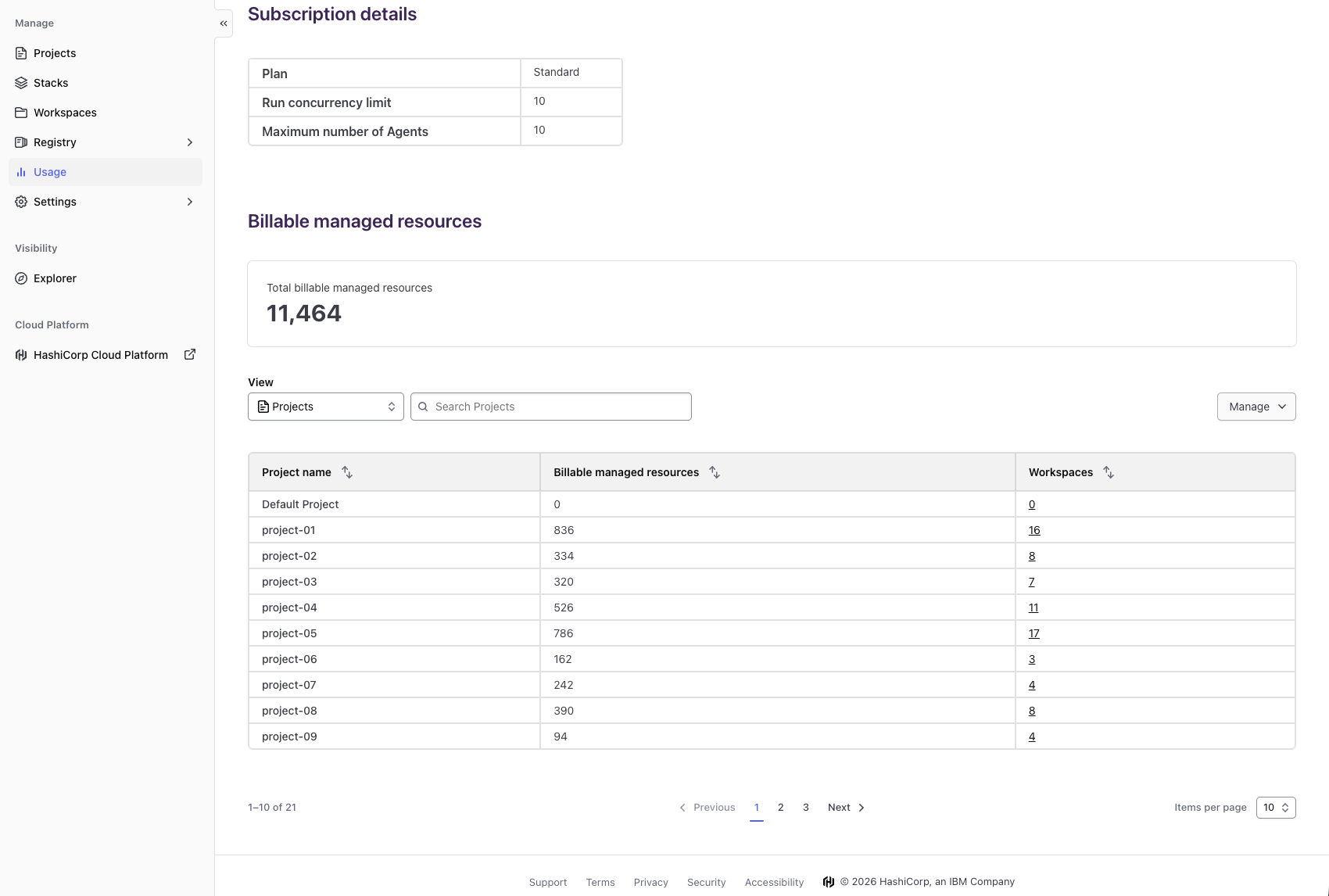
Organizations using resources under management (RUM)-based billing have long struggled to pinpoint where their infrastructure costs originate. Previously, HCP Terraform customers could only view total billable managed resources at the organization level, with no easy way to break down consumption by individual projects or workspaces. This lack of granularity made it difficult to estimate costs, forecast future spending, and identify which teams or environments were driving usage.
What’s New
With the general availability of billable resource analytics, HCP Terraform now offers a self-service view on the existing usage page. This new capability provides comprehensive visibility into resource consumption across the entire organization, showing current totals of billable managed resources broken down by project and workspace. Decision-makers can quickly see where spending is concentrated and take immediate action to optimize costs.
Key Benefits
- Cost visibility and predictability: Organizations can proactively manage infrastructure spending instead of reacting to unexpected bills. By identifying high-consumption projects and workspaces, owners can work with engineering teams to right-size resources, eliminate waste, and stay within budget.
- Data-driven decision making: Leaders can base infrastructure investments on actual consumption patterns rather than guesswork. Detailed breakdowns reveal which projects consume the most resources and where consolidation opportunities exist, enabling strategic allocation that aligns spending with business priorities.
Any user on a paid HCP Terraform plan can access the new view on the usage page to start exploring billable resource analytics.
Project-Level Remote State Sharing (GA)
Simplifying Data Sharing Across Teams
Platform teams managing large-scale infrastructure often face a trade-off when sharing state data: either open access widely, risking security, or enforce strict isolation that hinders collaboration. The new project-level remote state sharing capability resolves this dilemma. Previously, state sharing was only possible at the workspace level or across an entire organization, leaving gaps in flexibility and control.
What’s New
With project-level remote state sharing, administrators can now define access to state data at the project level. This allows teams within the same project to securely share resources and outputs without exposing data to other projects. The feature helps maintain fine-grained control over infrastructure data while enabling efficient collaboration across workspaces that belong to the same logical group.
Benefits
- Enhanced security: State data remains isolated between projects, reducing the risk of accidental exposure.
- Improved collaboration: Teams can reuse outputs and references across workspaces within a project without manual duplication.
- Scalable governance: Platform teams can define sharing policies at the project level, aligning with organizational boundaries.
Module Testing for Dynamic Credentials (GA)
Streamlining Credential Lifecycle Management
Dynamic credentials provide temporary, just-in-time access to cloud resources, but testing modules that use them has been cumbersome. Historically, developers had to create permanent credential stubs or rely on manual testing, which introduced security risks and slowed development workflows.
What’s New
Module testing for dynamic credentials is now generally available. This feature allows module authors to write and run tests using dynamic credentials in their CI/CD pipeline without needing long-lived secrets. It leverages Terraform’s testing framework to validate that modules correctly request, use, and rotate dynamic credentials, ensuring reliability and security.
Benefits
- Faster development: Authors can test modules in automated pipelines without manual credential setup.
- Reduced risk: Dynamic credentials are automatically rotated, minimizing exposure if a test environment is compromised.
- Improved confidence: Tests confirm that modules handle credential lifecycle correctly before deployment to production.
Project-Level Notifications (GA)
Fine-Tuning Alerts for Better Awareness
Notify teams about run failures and state changes has been possible at the workspace level, but managing notifications across many workspaces was tedious. Platform teams often needed to configure the same alert rules repeatedly, leading to notification fatigue or missed critical events.
What’s New
Project-level notifications are now generally available. Administrators can define notification configurations at the project level, which automatically apply to all workspaces within that project. Supported destinations include email, Slack, webhooks, and more. This reduces duplication and ensures consistent alerting for every workspace in the project.
Benefits
- Simplified management: One notification configuration applies to an entire project, saving time and reducing errors.
- Consistent alerting: All workspaces in a project receive the same notification rules, ensuring no team misses critical events.
- Reduced noise: Teams can tailor notifications per project, focusing on what matters most for their workflows.
Registry Tagging (Beta)
Organizing Modules and Providers
As organizations scale their use of community and private modules, finding the right module quickly becomes challenging. The Terraform Registry offered search and filtering, but lacked a flexible way to categorize modules beyond simple names and descriptions.
What’s New
Registry tagging is now available in beta. Users can assign custom tags to modules and providers in the Terraform Registry (both public and private). Tags are key-value pairs that allow teams to label modules by use case, compliance level, team ownership, or any other criteria. This makes discovery and governance easier.
Benefits
- Improved discoverability: Search for modules by tags such as “production,” “PCI-compliant,” or “team-platform.”
- Better governance: Platform teams can enforce tagging policies to ensure modules are properly categorized before use.
- Flexible categorization: Tags adapt to each organization’s unique taxonomy, supporting both simple and complex hierarchies.
Conclusion
These latest enhancements to HCP Terraform and Terraform Enterprise underscore HashiCorp’s commitment to providing comprehensive infrastructure lifecycle management. Billable resource analytics bring cost transparency, project-level sharing and notifications improve governance, module testing for dynamic credentials strengthens security, and registry tagging simplifies discovery. Together, these features help organizations reduce blind spots, make data-driven decisions, and maintain control over their infrastructure at scale.
For more details, visit the billable resource analytics section or explore the remote state sharing and project-level notifications capabilities. The registry tagging beta is available for all HCP Terraform and Terraform Enterprise users.